- #LEARN
- AI
- behaviour
- coaching
- computing
- general
- HTTCS
- inclusion
- leadership
- online safety
- pedagogy
- physical
- podcast
- programming
- teaching and learning
- tech
- Uncategorized
#LEARN AI algorithms binary book books clubs coding CPD critical thinking curriculum education encoding events fiction gender general girls hinterland interview interviews leadership learning ncce non-computing podcast programming python resources school teachers teaching technology writing

EQAITE: Evaluating Quality AI for Teaching Excellence
Schools, colleges and universities are now overwhelmed with choice when it comes to AI tools. Some institutions have grasped the nettle and are powering ahead with AI, others are quite rightly nervous about adopting the new and daunting technology while managing the new risks it presents. In response to these challenges, three educators have come…
Podcast S2E06 “What does inclusion look like in computing?”
New episode of the HTTCS podcast: Transcript below: ArtiFiciAL: Welcome to the podcast “How to Teach Computer Science”. My name is ArtiFiciAL and I will be introducing the podcast today, which was conceived and created by the brilliant Alan Harrison. I enjoy being an AI podcast host you know. I had to work my way…
Podcast S2 Ep5: “Will AI revive the art of tinkering?”
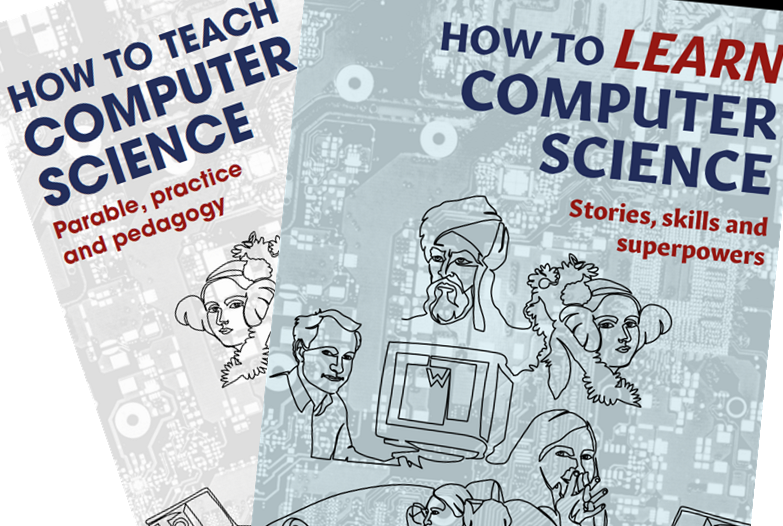
My discussion with Miles Berry and Becci Peters is live on all good podcast platforms and here: pod.httcs.online/e/s2e05 The transcript follows below. Alan: Hello, and welcome to How To Teach Computer Science the podcast. My name’s Alan Harrison, and I wrote the books how to teach computer science and how to learn computer science available…
You must be logged in to post a comment.